cybersecurity


Authorities in the Netherlands have arrested the co-owners of two related Internet hosting companies for operating IT infrastructure used by Russia to carry out cyberattacks, influence operations and disinformation campaigns inside the European Union. The two men were the focus of a 2025 KrebsOnSecurity story about how their hosting companies had assumed control over the technical infrastructure …

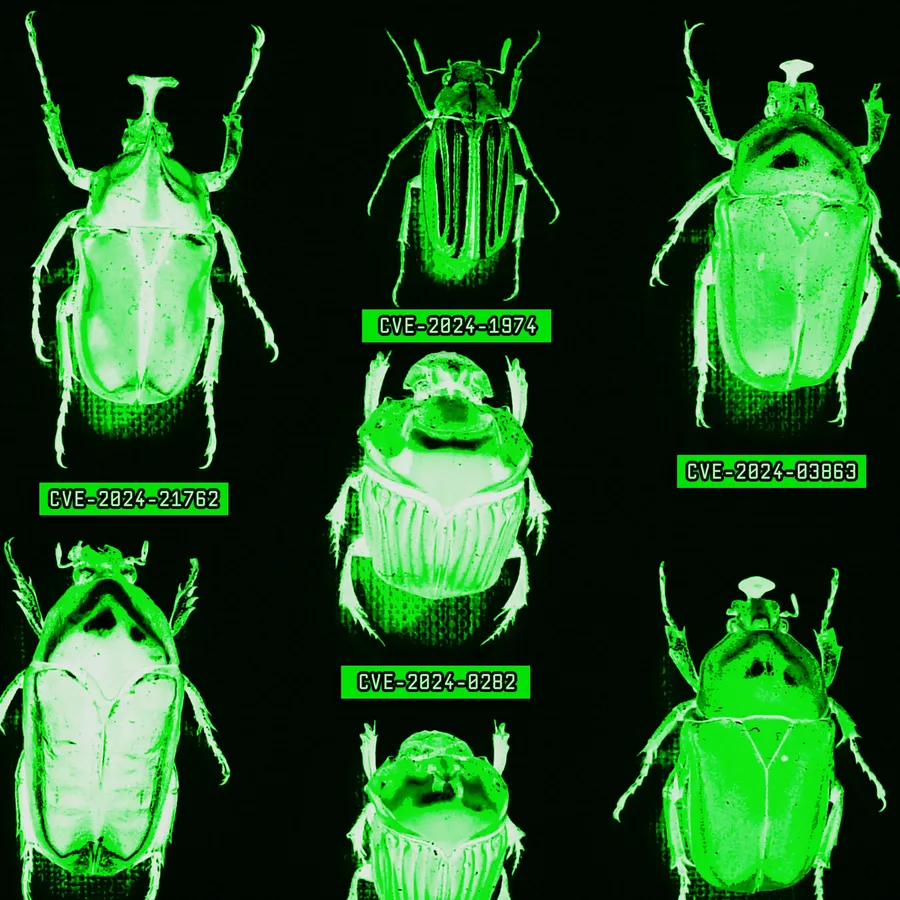
As attackers ramp up their AI exploit development, the search for software vulnerabilities is changing rapidly.

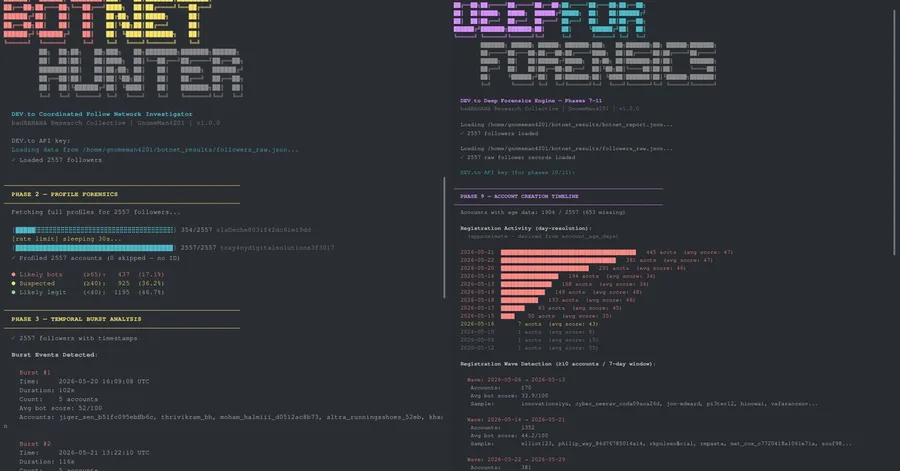
A full technical audit of a coordinated follower inflation network — methodology, findings, and a detection rule simple enough to run in one query. On May 19, 2026, I published "Found a Coordinated GitHub Follow Botnet" — a piece documenting a coordinated follower inflation network on GitHub. The next day, my DEV.to follower count started climbing. Fast. Date New Followers May 19 75 May 20 288 Ma…

I'm offering 5 free 20-minute security audits for SaaS founders this month - no pitch attached. Background : I've spent a decade in cybersecurity and built a security monitoring tool for solo founders and small SaaS teams. I want to talk to more founders in this position - even ones who'll never use my product - so I'm offering 5 free audits this month. What you get: I run a passive security scan…
Operational Technology (OT) is experiencing one of the most remarkable shifts in its history as increased OT and Information Technology (IT) systems converge to form unified, intelligent systems. The aim of this review article is to look at the most important technology trends that are currently changing the OT landscape and consider the impact of these on architecture, operation, and security fo…
International audience
6G paradigm enables massive network slicing for pervasive digitization across vertical industries, demanding scalable,sustainable, AI-driven zero-touch automation, particularly under non-IID conditions in live networks. This work introducesa cloud-native service-level agreement (SLA)-driven stochastic policy to guarantee a scalable and fast operation of constrainedfederated learning (FL)-based an…
With the increasing deployment of Reinforcement Learning (RL) for network optimization at the edge of wirelessnetworks, the RL workload emerges as a significant challenge. While the placement of general Machine Learning workloadsacross the cloud–edge continuum has been widely studied, existing solutions typically exclude RL techniques due to theirdistinct structure and operational requirements. I…
Sixth-generation (6G) wireless networks are expected to meet all the demands of the next decade, a feasibility that is onlypossible with advances in network design and management. This paper first proposes a unified resource management framework for a 6G-based network architecture that includes an Open Radio Access Network (O-RAN) deployment and then defines a hierarchical network energy control …


AI Prompt Injection, Drupal SQLi Exploitation, and Nmap for Hardening Today's Highlights Our top stories tackle AI-specific security with a fresh perspective on prompt injection, warn of active exploitation for a critical Drupal SQLi vulnerability, and offer a practical guide to network scanning with Nmap. These insights equip security professionals and developers with knowledge on emerging AI th…

If you've wired up an AWS CodeBuild project to pull source from GitHub via CodeConnections (formerly CodeStar Connections), you may have hit this error at the moment you call UpdateProject or trigger your first build: OAuthProviderException: User is not authorized to access connection arn:aws:codestar-connections:us-east-1:123456789012:connection/... The error wording is wrong in two different wa…

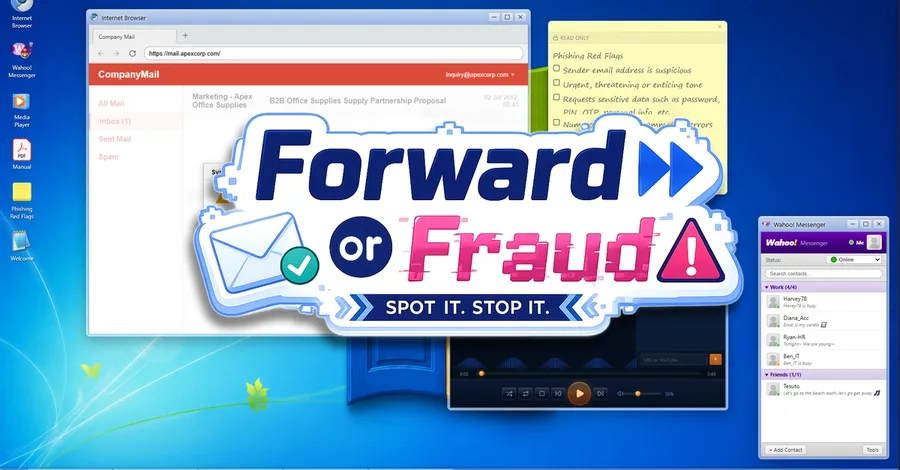
This is a submission for the Gemma 4 Challenge: Build with Gemma 4 What I Built "Forward or Fraud" is an immersive, gamified cybersecurity educational simulator disguised as a retro desktop operating system. Players roleplay as corporate employees navigating a typical work week. Using a fully simulated workstation, they must manage their daily tasks, inspect incoming emails, analyze their content…

Most AI coding tools are built to assist you. Rogue Studio is built to attack you — specifically, to attack the code it just wrote for you, find every vulnerability, and force itself to fix them before you ever see the output. Here's how I built the adversarial swarm architecture, and why I think this approach to AI-assisted security is underexplored. Why I built this I kept hitting the same wall…

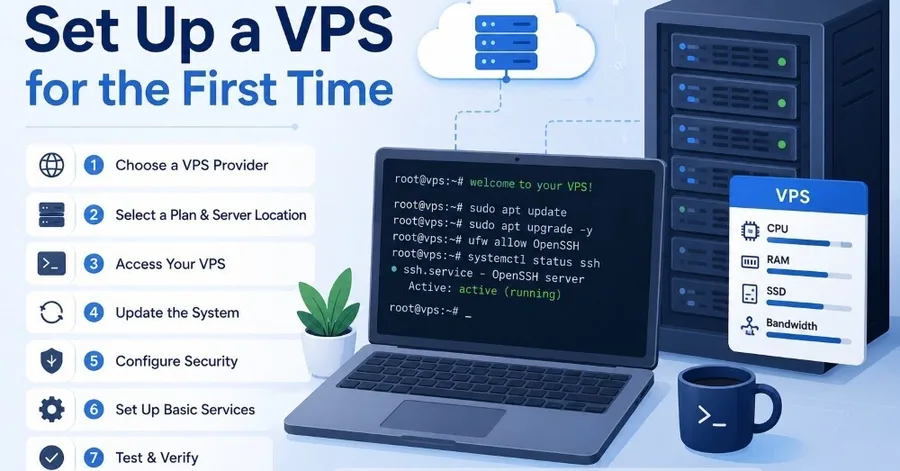
You just bought a shiny new VPS. You got an IP address, a root username, and a random password emailed to you. Logging in as root and dumping your code immediately is the fastest way to get your server hijacked by botnets within 2 hours. Let’s do it the right way instead. Here is a step-by-step walkthrough to get your virtual server up, running, and hardened against common security threats. Why y…

I built SecURL about six months ago during a stretch of evenings where I kept hitting the same frustration: running a security scan on a site and getting back either a wall of jargon or a narrow result that only checked one thing. securityheaders.com checks headers. SSL Labs checks TLS. Mozilla Observatory covers a bit more. But nothing gave you the full picture in one pass, ranked by what to act…
Hema Priya. T, LLM, School of Law, Vels Institute of Science, Technology & Advanced Studies, VISTAS, Pallavaram, Chennai Dr. S. Jenifer Stella, Assistant Professor, School of Law, Vels Institute of Science, Technology & Advanced Studies, VISTAS, Pallavaram, Chennai ABSTRACT Cybercrime has emerged as one of the fastest-growing forms of crime in India due to rapid digitalisation, increased …
We analyze the linearized dynamics of the validated late-time coherence-field kernel of Radial Coherential Dynamics (RCD), the bistable Allen–Cahn / Wright–Fisher reaction–diffusion equation whose coarsening behavior in expanding Friedmann–Robertson–Walker (FRW) backgrounds was established in prior work [1]. Computing the principal symbol of the operator governing small perturbations δC about a h…
 research.io
research.ioSign up to keep scrolling
Create your feed subscriptions, save articles, keep scrolling.