computer-science


React Server Components are now the default in Next.js and they’re shipping in TanStack Start. Whether you opted in or not, you’re going to encounter them in 2026. The good news: the TanStack approach makes RSCs feel like a tool you can opt-in for instead of a paradigm shift like in Next.js. Let’s look at RSCs in depth - Your component runs on the server. The server sends back the already-rendere…

After nearly 20 years leading teams in hospitality and logistics, I made a career change into software development. When it came time to build my portfolio, I made a deliberate choice: it would not be just a collection of screenshots and technology lists. It would be a working demonstration of how I think about software architecture. This is the story of how I built it, the architectural decision…

Async/Await in JavaScript: From Callbacks to Clean Code (2026) Async JavaScript has come a long way. Here's the complete picture — from callbacks to async/await and everything in between. The Evolution // ERA 1: Callbacks (2010-ish) — The "Callback Hell" getData ( function ( a ) { getMoreData ( a , function ( b ) { getEvenMoreData ( b , function ( c ) { getFinalData ( c , function ( finalData ) {…

Modern Angular applications rarely need just a dropdown. In real projects, a multiselect dropdown usually sits inside something more important: filters, dashboards, reporting tools, permission editors, workflow screens, admin panels, and data-heavy forms where users need to search, group, select, clear, validate, and keep state consistent. That is the context behind Stackline Angular Multiselect …

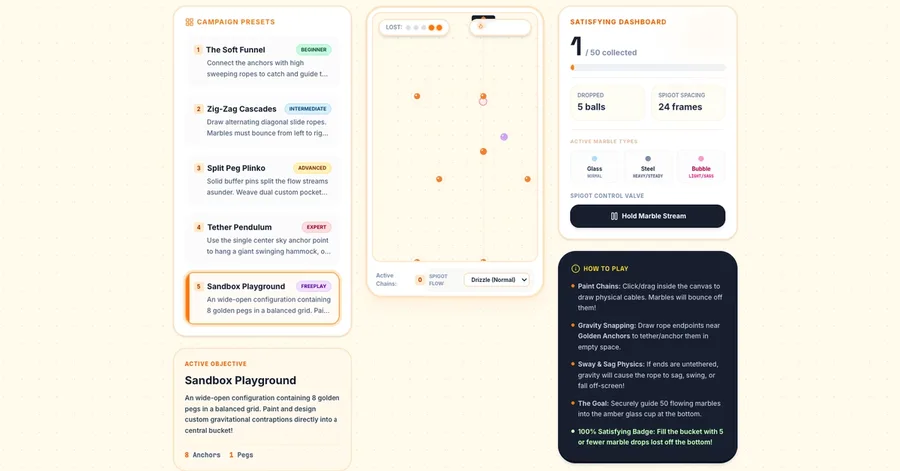
Physics-based browser games are nothing new, but creating something that feels truly organic, interactive, and sensorily satisfying remains a rewarding engineering challenge. In this technical blog post, we look under the hood of Gravity Paint – a gravity-aware sandbox puzzle where players paint rigid rope cables to funnel a stream of colorful glass, steel, and bubble marbles into an target colle…

5. Longest Palindromic Substring: Unraveling the Palindromic Puzzle 🧩 Hey fellow coders! 👋 Today, we're diving into a LeetCode classic that often stumps beginners but reveals a really elegant pattern once you spot it: the Longest Palindromic Substring problem. Don't let the fancy name scare you! We'll break it down piece by piece, find an intuitive way to tackle it, and emerge victorious with a n…

A beginner's honest walkthrough of Extract, Transform, Load using the GitHub API The post I Built My First ETL Pipeline as a Complete Beginner. Here’s How. appeared first on Towards Data Science .

The Problem We Were Actually Solving At Veltrix, we're known for our real-time treasure hunts – a complex feature that involves querying a massive graph database, processing high-frequency event streams, and returning results in under 100ms. However, when we started to onboard more clients and scale our infrastructure, our operators consistently hit the same problem: configuring the system to han…

The Problem Every sysadmin has been there: you SSH into a server and wait... and wait... 10 seconds later, you finally get a prompt. It's one of those small annoyances that wears on you over time. I ran into this again last week while troubleshooting a production server. The delay wasn't there before, something had changed. Common Causes After digging into this enough times, I've found these usua…

Most n8n AI workflow tutorials end at "it worked in testing." The gap between a demo and a production system handling 10,000 items/day with real money on the line is where the interesting problems live. At Chronexa , we've built 50+ multi-agent workflows for fintech compliance teams, legal document processing, AI SDR engines, and RAG-powered research assistants. Here's what we've learned about ma…


Claude Code forgets everything between sessions. You explain your project, your architecture, your preferences and next session it's ground zero again. I spent 45 minutes setting this up manually. Debugging ports, copying tokens, configuring MCP servers by hand. Then days debugging the Smart Connections integration. So I built ObsiForge, one command that does all of it: obsiforge init --name mypr…

TL;DR: We needed to caption 1.2M reconstructed event-camera frames using vision-language models for auxiliary supervision. The first run died at 340K from Anthropic rate limits. Putting Bifrost in front of three VLM providers cut the rerun cost by 22% and finished in 9 hours. So, the thing is, when you work at a neuromorphic vision startup, your training data looks strange. At Prophesee we accumu…

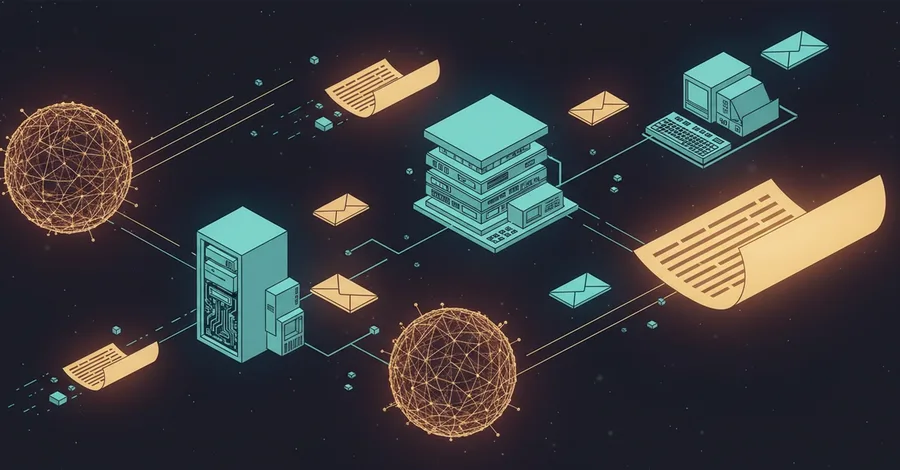
Messaging infrastructure has been boring for a decade. Queues, topics, exchanges — the primitives settled. Then AI agents arrived, and suddenly the assumptions that made messaging boring stopped holding. Messages are no longer just data. They are context. An agent will read your message, reason over it, call tools because of it, and generate responses whose token count you cannot predict at enque…

description: Most .cursorrules files are either too vague to help or too rigid to be useful. Here's what I found actually works after building rules for 10 different stacks. tags: cursor,ai,webdev,productivity I've spent a lot of time reading other people's .cursorrules files. Some are fantastic. Most are not. Not because the authors didn't try — but because there's a gap between what feels like …

⏱️ Reading time: 7-9 minutes 🎯 Difficulty: Beginner - Intermediate 📂 Themes: Computer Science, Binary, Memory, Performance What's inside? 🔍 The Problem — A CSS color that made me realize I understood nothing ⚡ Bits & Bytes — The two building blocks of everything 🔣 Hex & RGB — Why #FF0000 is red, and what those letters actually mean 🔤 ASCII & UTF-8 — How numbers become letters, emoji, and everythi…

ShellReq - Native API Client for VS Code & Terminal A lightweight, native API testing ecosystem designed directly around developer workflow and productivity. No context switching, no bloated UI, just fast API testing exactly where you code. Quick Links VS Code Marketplace: maheshshinde9100.shellreq-api-client GitHub Repository: maheshshinde9100/ShellReq NPM Package: shellreq Preview Why I Built S…

In this article, we will look at how the CockroachDB engineering team built this index and the challenges they faced.

Drag-drop upload, unguessable URLs (72 bits entropy), auto-deletes after 1h/24h, strict MIME allowlist + CSP sandbox. One docker compose up. MIT. 🔗 https://github.com/rogerhokp/tmpdrop 🌐 https://tmpdrop.solardev.online Why another one: public file hosts retain your data on infra you don't control + predictable URLs get scraped. tmpdrop is "0x0.st but on your own box" with a security posture I'm a…


After understanding composition, inheritance, and polymorphism, the next important step is learning how to define clear behavioral contracts between components. This is where interfaces and abstract classes become essential. They help answer one of the most important questions in system design: “What should this component be capable of doing?” without tightly coupling the system to a specific imp…
 research.io
research.ioSign up to keep scrolling
Create your feed subscriptions, save articles, keep scrolling.