malware
Executive Summary Cyble Research and Intelligence Labs (CRIL) has uncovered a targeted cyberespionage campaign leveraging social engineering and trusted infrastructure to establish persistent, covert access to victim systems. The attack is delivered via phishing emails containing a malicious LNK file disguised within a RAR archive, using a Russian humanitarian aid request form to exploit contextu…

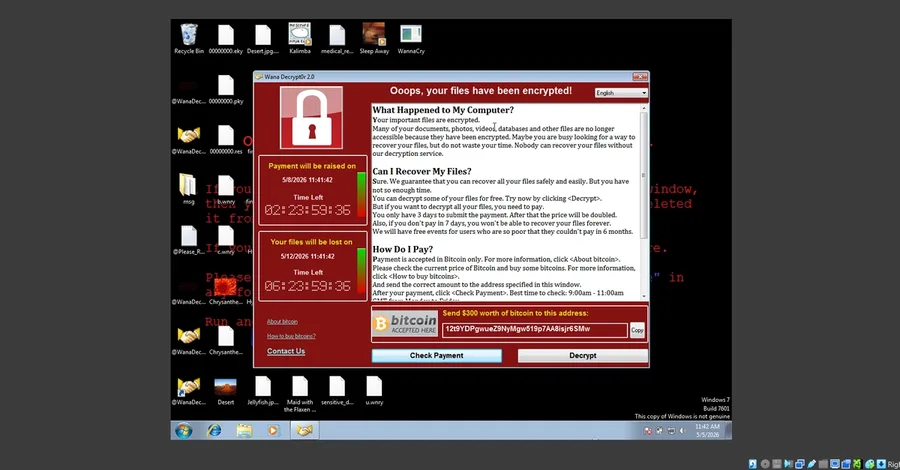
A hands-on technical breakdown of the WannaCry ransomware, the EternalBlue exploit, and why system patching is still critical today. Imagine it’s a typical Monday morning at a mid-size hospital. An older Windows computer in the Radiology department hasn't been updated in months. The hospital's network is completely "flat," meaning every computer can seamlessly talk to every other device on the ne…


Notable Changes Observed in Malicious LNK Files Distributed by Kimsuky Group Article Summary: The North Korean Kimsuky hacker group recently used malicious LNK files disguised as HWP documents to launch multi-stage attacks. They extended the attack chain by adding intermediate stages such as XML, VBS, and PS1 files to evade detection. The attack creates hidden folders, registers scheduled tasks f…

Executive Summary CRIL (Cyble Research and Intelligence Labs) has been tracking a sophisticated commodity loader utilized by multiple high-capability threat actors. The campaign demonstrates a high degree of regional and sectoral specificity, primarily targeting Manufacturing and Government organizations across Italy, Finland, and Saudi Arabia. This campaign utilizes advanced tradecraft, employin…
Key Takeaways Threat Actors (TA) use social engineering to trick users into executing a malicious LNK file disguised as a PDF document, leading to malware infection. The malware then leverages PowerShell to download and execute malicious payloads from a GitHub repository while ensuring persistence through registry modifications. The malware extracts browser cookies by enabling remote debugging, b…
Key Takeaways BTMOB RAT is an advanced Android malware evolved from SpySolr that features remote control, credential theft, and data exfiltration. It spreads via phishing sites impersonating streaming services like iNat TV and fake mining platforms. The malware abuses Android’s Accessibility Service to unlock devices, log keystrokes, and automate credential theft through injections. It uses WebSo…
Key Takeaways Cyble Research and Intelligence Labs (CRIL) identified malware being spread via a ZIP file containing an .LNK file disguised as a PDF and an XML project file masquerading as a PNG to trick users into opening it. The filename suggests that the malware is likely targeting organizations in Vietnam, particularly in the Telemarketing or Sales sectors. The LNK file creates a scheduled tas…
The ransomware attack that hit supply chain management platform Blue Yonder and its customers last month was the work of a new ransomware group called “Termite.” Cyble Research and Intelligence Labs (CRIL) researchers have examined a Termite ransomware binary and determined that Termite is essentially a rebranding of the notorious Babuk ransomware . The Termite leak site claims seven victims so f…

Key takeaways Cyble Research and Intelligence Labs (CRIL) uncovered a sophisticated multi-stage malware attack originating from an archive file that contains a malicious LNK file. The lure document observed in the campaign indicates that the Threat Actor (TA) is targeting job seekers and digital marketing professionals, especially those involved with Meta Ads. The malware employs several techniqu…
Key Takeaways Since June 2024, a new Android Spyware campaign has been identified targeting individuals in South Korea, leveraging an Amazon AWS S3 bucket as its Command and Control (C&C) server. The Spyware is capable of exfiltrating sensitive information from an infected device, including SMSs, contact lists, images, and videos. The stolen data, stored openly on the S3 bucket, suggests poor ope…

Key Takeaways Cyble Research and Intelligence Labs (CRIL) identified an active Gamaredon campaign targeting Ukrainian military personnel through spear-phishing emails. The emails include malicious XHTML attachments, which, when opened, execute obfuscated JavaScript code that downloads a malicious archive to the victim’s system. This archive contains a Windows shortcut (LNK) file that, when trigge…

Key Takeaways Cyble Research and Intelligence Labs (CRIL) observed an interesting campaign that utilized malicious LNK files, which could potentially be distributed via spam email. The Threat Actor (TA) behind this campaign uses human rights seminar invitations and public advisories as a lure to infect users with a malicious payload. This campaign highlights the attackers' sophistication by embed…
Key Takeaways A new Android Banking Trojan, “Antidot,” masquerading as a Google Play update application, displays fake Google Play update pages in multiple languages, indicating a wide range of targets. Antidot incorporates a range of malicious features, including overlay attacks and keylogging, allowing it to compromise devices and harvest sensitive information. Antidot maintains communication w…
Key Takeaways Cyble Research and Intelligence Labs (CRIL) has uncovered a novel phishing campaign tailored to cryptocurrency users. This campaign was deploying a well-known FatalRAT along with additional malware such as Clipper and Keylogger. The Threat Actors (TAs) orchestrating this campaign employ the DLL side-loading technique to load and execute FatalRAT, Clipper, and Keylogger modules. Fata…